The SpiKey attack: How to copy keys using sound
Por um escritor misterioso
Descrição
The SpiKey attack: How one can copy a key using a phone recording of the sound of the clicks the key makes during insertion into a lock.

Spike - Super Mario Wiki, the Mario encyclopedia
Threat Tracking: Tracking Threats Across the Dark and Clear Web - Flare
7 Best File Integrity Monitoring (FIM) Tools for 2023 (Paid & Free)

The SpiKey attack: How to copy keys using sound

The SpiKey attack: How to copy keys using sound

Using Artificial Intelligence To Counter Zero-Day Cyber Attacks: A Security Imperative During The COVID-19

The 23 Most Rare and Expensive Pokémon Cards
Ableton Live 12 Review - More MIDI, more GUI, more sound
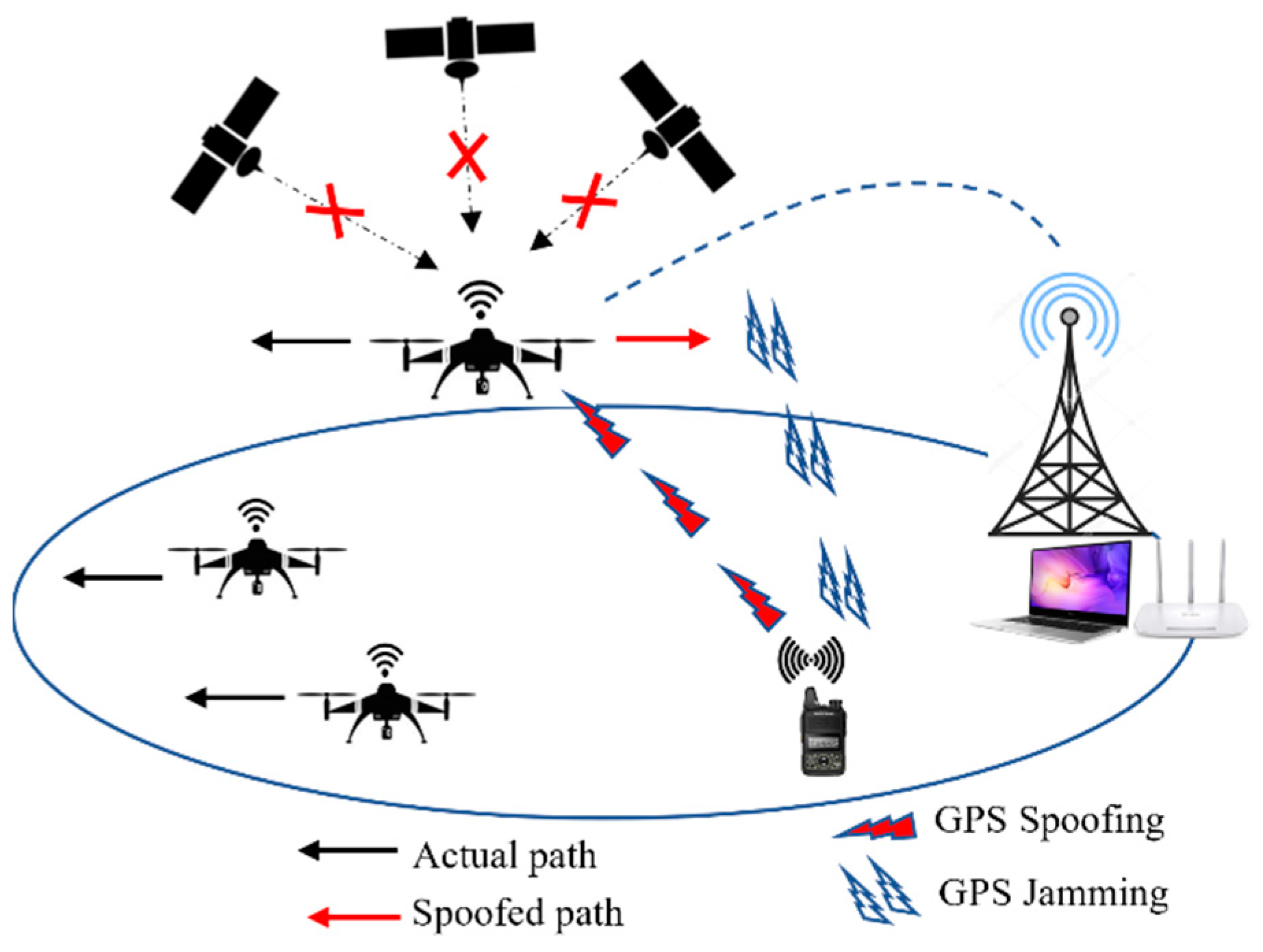
JSAN, Free Full-Text

Experimental data on neurons with spike frequency adaptation (SFA) and

Identity-Based Attacks and Hands-on-Keyboard Activity on the Rise
de
por adulto (o preço varia de acordo com o tamanho do grupo)







